Cyber Security
Cyber Insurance and Patch Management: Best Practices to Reduce Risk
Software Updates and Patch Management: What Insurers Expect and How to Deliver
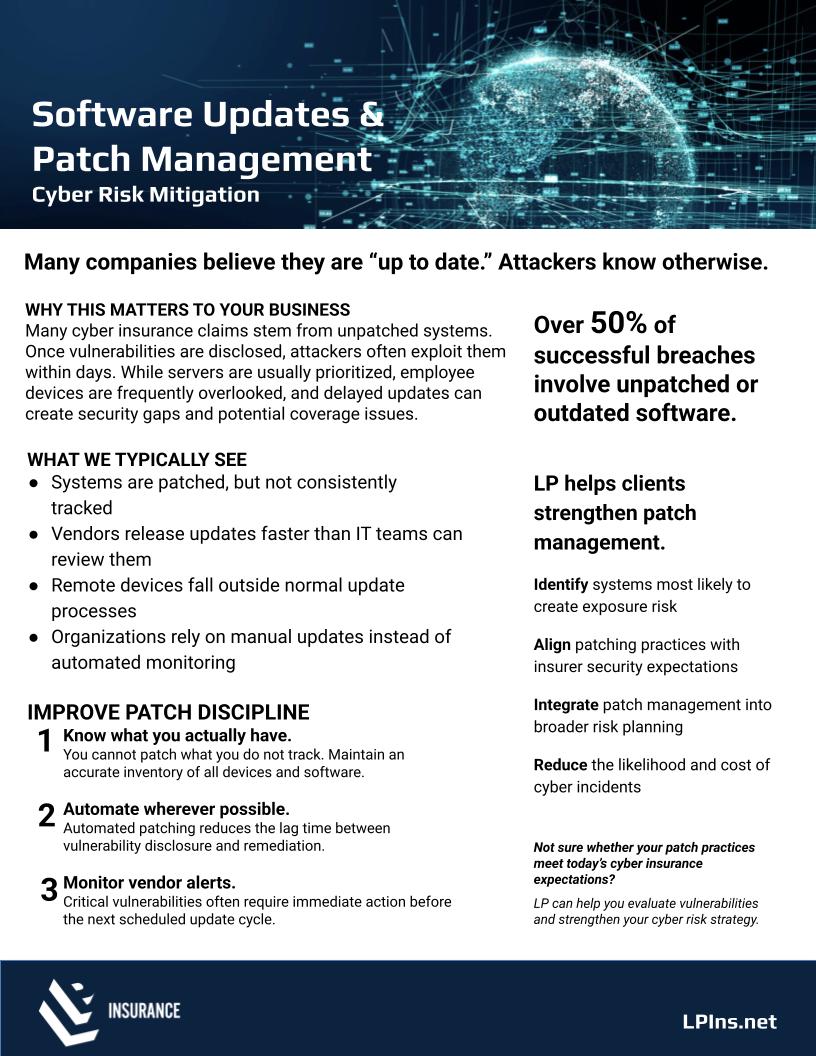
At LP Insurance, we take our role as guardians seriously. When clients ask why cyber insurers care so much about software updates, the answer is simple: unpatched systems open the door. Over 50% of successful breaches involve unpatched or outdated software. Strong patch management does more than reduce incidents—it protects your ability to get and keep cyber coverage on the right terms.
Why patching matters to your business
- Attackers routinely weaponize disclosed vulnerabilities within days.
- Underwriters now verify patch discipline as a core control. Gaps can trigger higher premiums, sublimits, exclusions, or outright declinations.
- Servers get attention, but employee devices, remote endpoints, and third‑party applications (browsers, Java, Adobe, collaboration tools) often fall behind—creating coverage and compliance issues.
What we typically see
- Patching happens, but isn’t consistently tracked or reported.
- Vendor updates arrive faster than IT teams can review and test.
- Remote and hybrid devices sit outside normal update windows.
- Manual processes replace automated monitoring and enforcement.
3 steps to improve patch discipline
- Know what you actually have You can’t patch what you don’t track. Build a living inventory of all hardware, operating systems, and software—including versions and end‑of‑life status. Align inventory fields with what insurers request (asset count, OS versions, EOL flags, last patch date).
- Automate wherever possible Use centralized tools (RMM/MDM/endpoint management) to deploy OS and third‑party patches on a schedule with exceptions for emergency updates. Enforce reboot policies and create automated reports for compliance and insurer documentation.
- Monitor vendor alerts Subscribe to security advisories and CISA’s Known Exploited Vulnerabilities (KEV) list. Define “critical” and “high” severities, and set SLAs (e.g., critical within 72 hours; high within 7–14 days). Document emergency changes and compensating controls when delays are unavoidable.
How insurers evaluate patch management
- Application scope: Does your process include OS and third‑party apps across servers, workstations, and remote devices?
- Timeliness: Are there SLAs for different severity levels? Can you show last‑applied dates?
- Coverage: What percentage of endpoints are compliant at any time?
- Evidence: Can you provide screenshots, reports, or logs demonstrating patch status and exceptions?
- Governance: Is there a written policy, change control, and executive oversight?
Quick wins you can put in place this month
- Turn on automated updates for OS and browsers where safe and test critical apps first.
- Enable cloud management for remote devices; require devices to check in before accessing sensitive data.
- Standardize a monthly patch window, plus an “as‑needed” window for critical KEV items.
- Track EOL software and plan replacements before renewal.
- Generate a monthly patch compliance report for leadership and your broker.
Use our one-page Software Updates & Patch Management flyer to validate your approach and brief stakeholders. It distills the essentials your insurer expects and the steps that reduce both risk and cost.
We’ll walk with you If you’re unsure whether your current patch practices meet today’s cyber insurance expectations, our team can help you evaluate vulnerabilities, align SLAs with underwriting, and strengthen your cyber risk strategy—so you can focus on growing the business you’ve worked hard to build.
- Download the Printable Flyer
- Book a 20‑Minute Cyber Patch Readiness Review
FAQs
While requirements vary, many underwriters look for critical patches within 72 hours and high‑severity within 7–14 days, with documented exceptions and compensating controls.
Yes. Browsers, plug‑ins, productivity, and collaboration tools are common attack paths and are often checked during underwriting reviews.
Use cloud‑based management, require regular check‑ins, and enforce update and reboot policies before remote access to sensitive systems.